When it comes to IT security, companies think first and foremost of virus scanning and firewalls. These tools already make a significant contribution to safety. However, this is not enough for sustainable prevention. Especially in order to protect against cyberattacks, it is important to know all the devices and applications on the network and to keep all software up-to-date. Around a fifth of the hardware and software in a company is “shadow IT”. These systems, whose use the IT department is unaware of, pose a risk to the security of the corporate network. In addition, uninventoried software prevents licence management from being legally compliant. This can only be solved with a SAM software to complete and record the entire IT infrastructure.
“With the right mix of methods to inventory their IT infrastructure, companies significantly increase IT security and license compliance. This is especially true when inventory is paired with automated deployment for applications, patches, and operating systems. ”
Benedikt Gasch
CTO DeskCenter Solutions AG
Enhanced Security through SAM software
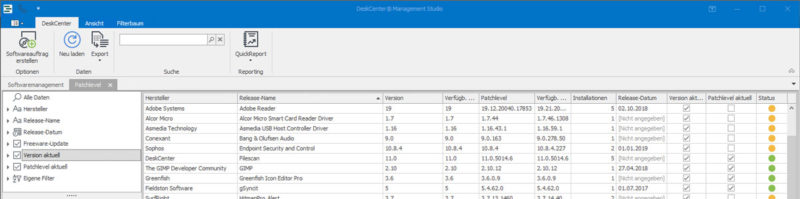
Through a fully inventoried IT infrastructure, companies successfully address security risks. Because it is the basis for automatic analysis of version and patch status. Ideally, this is done with the use of a software asset management (SAM) solution that compares all installed applications with a security database on a daily basis and lists its potential risks. Modern solutions also allow for software distribution and the ability to uninstall directly from the overview. This allows an outdated patch status to be updated or unauthorized software to be removed directly, thus immediately closing any security gaps.
The agony of Method Choice
Companies can use it to inventory a combination of agent-based and agentless capture methods. The selection includes device type (mobile device, fixed workstation computer, peripheral device), area of application (office, home office, the field) and the use of virtual systems.
For example, if access rights are granted centrally, inventory via remote access and services is possible. However, much of the hardware should be firmly connected to the network and therefore easily accessible. Then, the inventory solution can be accessed with administrative rights via services of the respective devices.
With a high proportion of mobile devices, agent-based detection should also be used. Because it also captures devices that connect to the company network on an irregular basis via a locally installed agent. The agent then reports their inventory data in certificate-based communication to the respective communication points in the data center or in the cloud– ideally without a VPN.
Servers and virtual worlds detect by SAM software
It is important that the SAM software detects which devices access terminal and Citrix servers or receive an IP address from the DHCP server infrastructure. This allows the unknown devices from “shadow IT” or any previously unrecorded BYOD devices to be uncovered.
Special consideration should be paid to the inventory of virtual assets. Rash deployment of virtual machines and associated server applications such as SQL can become a risk in the license audit, since the systems in virtual environments are subject to different metrics and rules. A sophisticated SAM solution is able to detect server license metrics from various manufacturers as well as access licenses for virtual environments and hosts. It also enables virtualization technology, such as VMware ESX, to be inventoried.
Last but not least, the IT infrastructure is part of a complete recording of devices that never go to the network for safety purposes as well as any peripheral devices such as telephone systems or printers. The former can be recorded “offline” via an inventory tool on a USB stick, the latter are automatically recorded via SNMP. Passive components such as monitors or docking stations should be supplemented manually for a complete picture of all assets.
Conclusion
Many companies are still a long way from the complete inventory of their entire IT infrastructure. It is the basis for successful IT management in order to achieve the highest possible level of security for systems and compliance and an optimal cost-benefit ratio.
